Living in Southern Alberta, we are all too familiar with the wind and the dust it carries. While we see it on our cars and windows, most Lethbridge computer users don’t realize that the same fine grit is slowly accumulating inside their technology. At Y-Not Tech Services, we’ve found that a significant portion of “slow computer” complaints aren’t actually caused by old age, but by environmental factors. [Read more…]
Lethbridge Cybersecurity Checkup: Protect Your Business Before 2026

As we head into 2026, Lethbridge businesses face a digital landscape that’s more connected—and more vulnerable—than ever before. Whether you run a cozy café on 13th Street, a growing accounting firm, or a bustling retail shop, your business relies on technology every single day. And with that reliance comes risk. [Read more…]
Why Computer Maintenance Matters for Lethbridge in 2025 | Y-Not Tech Services

Let’s be honest—most of us don’t think about our computers until something goes wrong. That spinning wheel of doom, the mysterious error message or, worse, the dreaded blue screen. Sound familiar? Here in Lethbridge, Alberta, where winters are cold and our reliance on technology runs hot, keeping your computer in top shape isn’t just a nice‑to‑have—it’s essential. Whether you’re running a small business downtown or managing your family’s digital life at home, regular computer maintenance can save you time, money and a whole lot of stress in 2025. [Read more…]
5 Signs Your Lethbridge Business Needs IT Support | Y-Not Tech Services 2025
Running a small business in Lethbridge is no small feat. Your computers, network, and software are the backbone of your operations, so when technology starts acting up it can quickly cost you time, revenue and peace of mind. As 2025 unfolds and digital demands grow, ignoring the early warning signs can turn minor glitches into major problems. In this article we’ll explore five clear signs that it’s time to bring in professional IT support for your business and how Y-Not Tech Services can help keep your systems running smoothly. [Read more…]
Avoid Tech Support Scams Lethbridge 2025 | Protect Seniors & Businesses
Tech support scams are on the rise across Canada, and Lethbridge residents—especially seniors and small business owners—are increasingly targeted. These scams are designed to look legitimate, sound urgent, and trick you into handing over money or access to your computer. The good news? Once you know what to look for, these scams are easy to spot and avoid. In this guide, we’ll walk you through the most common tech support scams in 2025, share real warning signs, and show you how to protect yourself, your loved ones, and your business. [Read more…]
Data Backup Solutions Lethbridge 2025 | Protect Your Business & Home | Y-Not Tech
Why Data Backup Matters in 2025
Lethbridge residents and small business owners have become more reliant on digital data than ever. Customer records, invoices, family photos, creative projects and more all live on hard drives and cloud services. Unfortunately, hard drives fail, laptops get stolen, and malware can encrypt or delete files without warning. In 2025, ransomware attacks, power outages, and even simple human errors continue to threaten our digital lives. Without a backup, recovering lost data can be impossible or prohibitively expensive. [Read more…]
Computer Upgrade Guide 2025 | Lethbridge Business & Home Users | Y-Not Tech

Planning Your Next Computer Upgrade in Lethbridge: A 2025 Guide for Businesses and Home Users
When was the last time you upgraded your computer? For many homes and small businesses in Lethbridge, Alberta, computers are like faithful workhorses — they get the job done until one day they don’t. Software gets slower, support for your operating system ends and the cost of repairs starts to add up. Technology moves fast, and 2025 brings new demands: cloud apps need more RAM, video calls require better webcams and processors, and cyber threats exploit outdated hardware. Planning your next computer upgrade isn’t about chasing the latest gadget; it’s about ensuring your tools can keep up with your life and business and that your data stays safe. [Read more…]
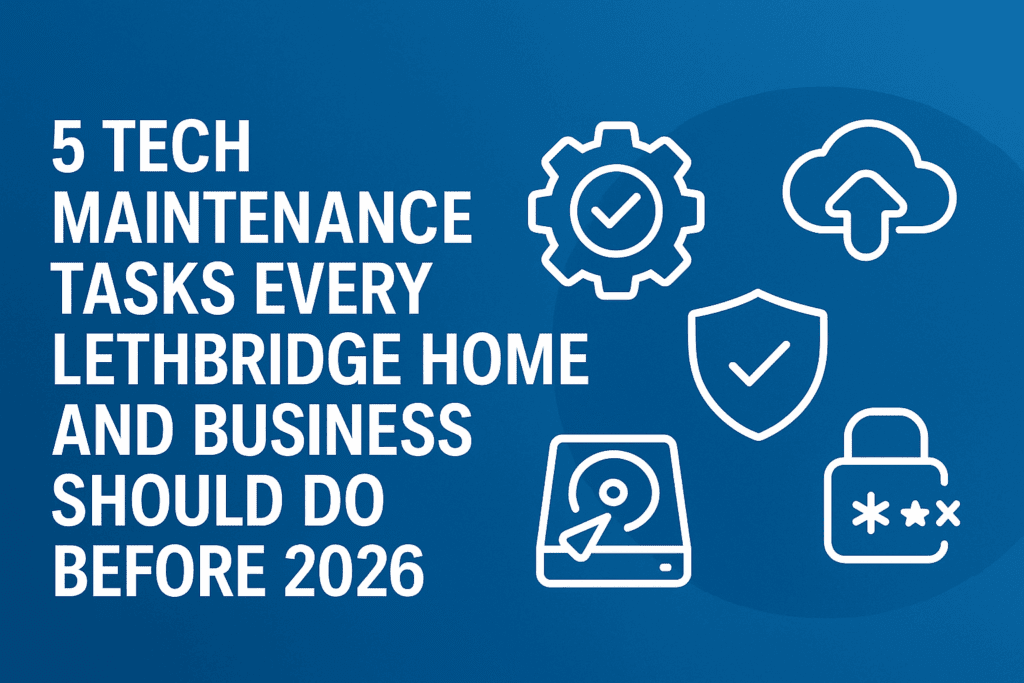
5 Tech Maintenance Tasks Every Lethbridge Home and Business Should Do Before 2026
As we approach the end of 2025, there’s no better time to give your technology a little TLC. Whether you’re a home user trying to keep your personal computer running smoothly or a small business owner managing multiple devices, regular tech maintenance isn’t just smart—it’s essential for your security, productivity, and peace of mind. [Read more…]
The Problem With “Forgotten” IT Devices | Y-Not Tech Services – Lethbridge, AB IT Support
The Problem With “Forgotten” IT Devices
Every business has those IT devices tucked away in storage rooms, old drawers, or even still sitting on your network unnoticed. Forgotten devices may seem harmless, but they can pose significant risks to your business’s security. Let’s take a closer look at why these “forgotten” devices are more of a ticking time bomb than a harmless relic of the past. [Read more…]
Why Safeguarding Your Backups Is Just as Important as Backing Up Your Data | Y-Not Tech Services – Lethbridge, AB IT Support
Why Safeguarding Your Backups Is Just as Important as Backing Up Your Data
Every business owner knows the importance of backing up their data. You’ve likely heard horror stories about companies losing everything due to unexpected disasters, malicious attacks, or human error. But here’s the thing many people don’t think about: backups themselves need protection.
Whatever jeopardizes your primary data – malware, theft, or natural disasters – can also take out your backup. [Read more…]
- 1
- 2
- 3
- …
- 17
- Next Page »